Everything you've been told about app security might be about to change. If you've ever felt uneasy about where your apps come from, Google's new approach to sideloading on Android aims to offer a middle ground, balancing user freedom with enhanced protection. Here's how Google's 'safer' sideloading is set to work, and what it means for you.
Sideloading Restrictions Are Coming to Android
Google announced plans to significantly limit app installations from outside its official Play Store. This move, designed to combat malicious apps that often mimic legitimate ones, will require third-party app stores and developers to register specific details with Google and pay a fee. While these restrictions begin rolling out in select countries later this year and globally in 2027, Google is introducing a new process to ease the transition for users who still wish to sideload.
This isn't just about making things harder; it's a direct response to the rise of malware disguised as popular applications. Think of someone trying to install a modified version of a popular game, only to find their device infected with spyware. The goal is to make it much tougher for bad actors to distribute harmful software.
However, this shift has sparked debate. Developers worry about increased privacy burdens and potential costs, while some users are concerned about losing the flexibility to install apps not available on the Play Store, perhaps for niche purposes or older device compatibility. Users might also want to install apps that customize their phone's behavior in ways Google doesn't officially support, like advanced call recording or system tweaks.
Recognizing these concerns, Google is implementing a compromise: an 'advanced flow' setting that introduces deliberate friction, aiming to prevent impulsive malware installations. This new process is designed to protect the average user while still offering a pathway for those who understand and accept the risks involved.
A New Sideloading Workaround
So, here's how Google's 'safer' sideloading process will actually function. Instead of a simple toggle, you'll engage in a multi-step procedure designed to ensure you're making a conscious decision. This isn't a one-time setup; you'll need to re-authenticate periodically, but the initial activation is designed to be a thorough process.
To enable this advanced flow, you'll first need to activate Developer Mode on your Android device. Then, you must confirm that you're not being pressured into disabling security measures - a crucial step, as scammers sometimes try to coerce users into this during a malicious installation. After this, you'll need to restart your phone. This reboot is important; it helps close any potential remote access tools or communication channels that bad actors might be using to influence your decision or control your device during the process.
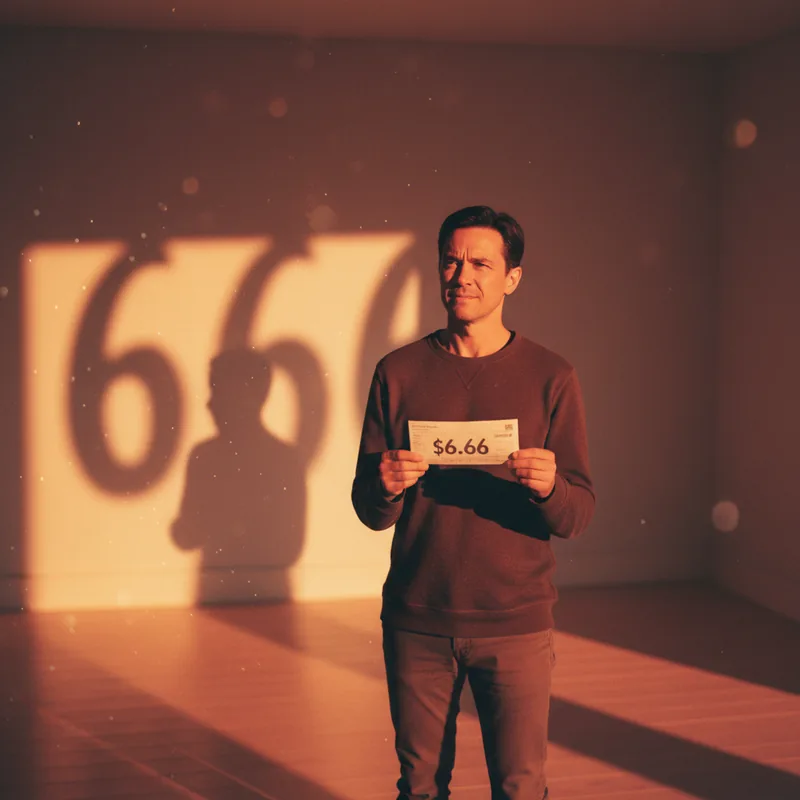
The real hurdle comes next: a mandatory 24-hour waiting period. Once that day has passed, you can return to your device settings. Here's how Google's 'safer' sideloading requires you to authenticate the change, typically using your device's PIN or biometric data. You'll then need to explicitly acknowledge the risks associated with installing apps from unverified sources. After this confirmation, you'll be able to sideload apps from unverified developers for a period of seven days, with the option for indefinite access if you continue to re-authenticate. This new system aims to make users pause and consider the implications before proceeding, effectively disrupting the urgent tactics often employed by those distributing malware.
This workaround is expected to be available starting in August, giving users a chance to adapt before the developer registration requirements fully come into play. It's a significant shift, and understanding here's how Google's 'safer' sideloading works is key to navigating the evolving Android app ecosystem.