It's 3:17 AM. You just woke up, a jolt of anxiety running through you. You reach for your phone, not to check the time, but to quickly delete that incriminating message you sent earlier on Signal. You even go a step further, uninstalling the app itself, thinking you've covered your tracks. It feels like a foolproof plan, right? This scenario might sound like something out of a spy thriller, but it highlights a real-world concern: just how secure are your supposedly deleted messages?
Understanding Signal's Security
Signal is renowned for its robust end-to-end encryption (E2EE). In simple terms, this means your messages are scrambled from the moment they leave your device until they reach the intended recipient. Think of it like a secret code that only you and your conversation partner possess the key to decipher. Even if someone were to intercept the message mid-transit - a hacker, a snooping internet provider - all they'd see is an indecipherable jumble of code. This level of security makes Signal a popular choice for those seeking private communication, a stark contrast to the government's infamous use of the app for war planning discussions last year.
However, E2EE, while powerful, isn't an impenetrable shield. It makes it significantly harder for unauthorized parties to read your messages without your unlocked device or app. But, as recent events have shown, difficult is not the same as impossible. This is a crucial reminder that no digital communication is entirely impervious to determined external forces, no matter how secure the platform claims to be.
The FBI's Ingenious Data Recovery
In a surprising turn of events, the FBI recently managed to extract deleted Signal messages from a defendant's iPhone, as reported by 404 Media. The situation was complicated by the fact that the user had not only deleted their messages but had also removed the Signal app entirely from their device. Logically, one might assume that deleting the app would sever any connection to past conversations. Yet, investigators found a way around this digital fortress.
Here's where it gets interesting: the FBI didn't need to breach the Signal app itself. Instead, they were able to access fragments of incoming messages directly from the iPhone's push notification database. It's a detail that might surprise many iPhone users, as these alerts are often transient. Notifications typically linger in the Notification Center until manually cleared or until the app is opened, offering a temporary window for data capture.
This revelation stemmed from a case involving alleged property vandalism and the setting off of fireworks at the ICE Prairieland Detention Facility, where an officer was shot. During the trial, it emerged that any application granted permission to display previews and alerts on the Lock Screen will store snapshots of that information within the device's internal memory. Consequently, investigators could retrieve messages the defendant had received, even though the messages were set to auto-delete within Signal and the app was no longer installed.
This isn't a vulnerability exclusive to Signal. Think about the cascade of alerts your phone receives daily: text messages, calendar reminders, news bulletins, social media direct messages, and even purchase confirmations. If an app has permission to show previews on your lock screen, those snippets of information could be preserved. For anyone with the right surveillance technology, this creates a potential goldmine of data, regardless of whether your phone is locked or unlocked.
Consider a scenario where someone receives a sensitive work-related message via Slack or a confidential health update through a medical app. If these apps display previews on the lock screen, even after deletion or app removal, fragments of that data might remain accessible through the notification cache. Another example could involve financial apps; if a transaction alert with preview enabled is deleted, the notification log might still hold a record of the purchase amount and merchant.
Protecting Your Data from Snooping Eyes
The good news is that knowing about this potential vulnerability empowers you to take proactive steps. Signal itself offers a straightforward solution within its settings to mitigate this risk.
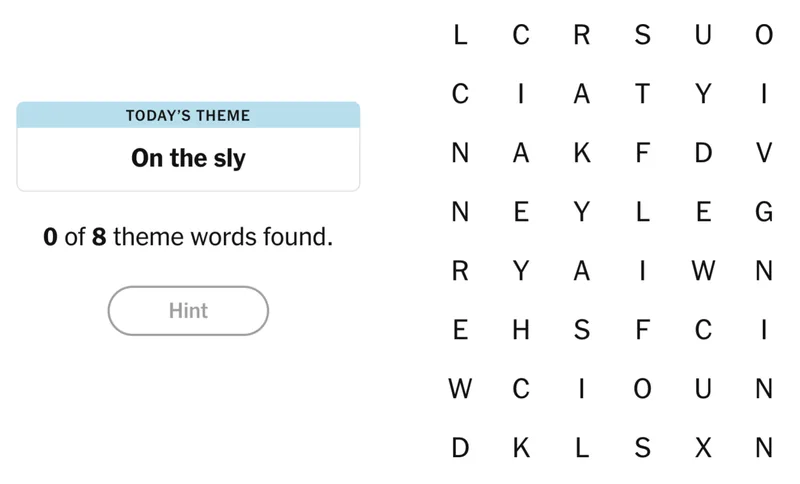
To enhance your privacy, open the Signal app and navigate to your profile icon in the top-left corner. From there, select "Settings." Within the settings menu, find the option for Notification Content. You have a few choices:
- "No Name or Content": This is the most secure option. It blocks all message details from appearing in notifications, meaning anyone glancing at your alerts will only see that you received a Signal message, without any sender information or content.
- "Name Only": This setting will display the sender's name but hide the message content. It offers a balance between knowing who contacted you and maintaining message privacy in notifications.
Choosing "No Name or Content" is the most effective way to prevent sensitive information from being exposed via the notification database. While "Name Only" can be convenient, remember that an intruder could still see who is messaging you if they gain access to your phone's alerts.
Ultimately, while Signal's end-to-end encryption is a powerful tool, it's wise to be aware of how your device and its operating system handle notifications. By adjusting your Signal settings, you can add an extra layer of defense, ensuring that even deleted messages remain private.